
Public charging stations at airports, parks, and coffee shops can be lifesavers when your phone battery is dying. As an IT Professional and Security conscience individual, I warn everyone I can. Thieves can steal your information depending on how and where you charge your devices through a technique known as ‘juice jacking.’
“Juice jacking is basically placing kiosks or other charging stations that look like they’re just going to give you power, but in fact, also have a malicious data component to go along with it,” (Wikipedia Source)
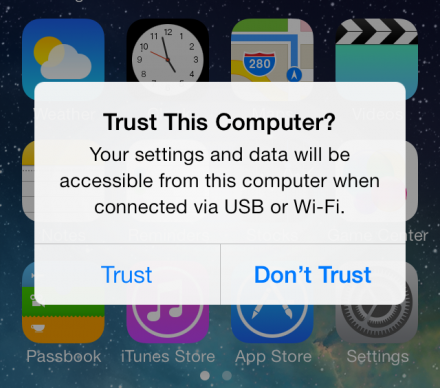
Just by plugging a smartphone into a compromised USB charger, a device can become infected.
In today’s digital world we all live and die by our phones. We have everything is on them. If you know me at times you can catch me charging one of my phones in public.
“95% of everything I have is on My Phone: Banking, flight numbers, everything,” said one of my close friends, who uses his smartphone similarly to a personal computer.
According to recent research performed by PhD students at MIT. Once hackers get access to a smartphone, they can secretly control it without the phone’s owner knowing.
Protecting your device from juice jacking can be as simple as the cord you use to charge your phone. Some tech stores and websites sell power-only USB cables. These kinds of cables will only transmit power, and nothing else, rather than that data connection in addition to that.
I do recommend purchasing a USB DataBlocker Adapter for your USB Cable. These DataBlockers allow you to charge your phone without any risk of hacking / uploading viruses.
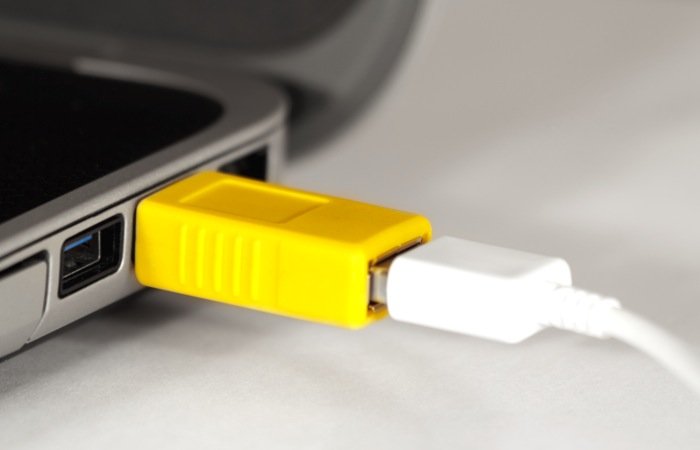
Here are the links to purchase from Amazon and Lazada
I also recommends charging a backup battery at public charging stations instead of the actual phone. Once the battery is juiced up, the phone can be connected to the battery to be charged.
No data will be transferred.
Typically, wall outlets are much safer than USB ports, since they only supply electricity.
I always advise, collegeues and friends before charging a smartphone in public, people should ask themselves a few questions:
“Does anyone have access to what’s behind that charging station? Does anyone have the possibility to put in a computer that would exploit your device?”
If the answer is “yes,” or you are unsure, then the possibility is there.






